Remote Browser Isolation: What is it & How it Really Works
5 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

As technology and the internet gets more advanced, so do the threats that come with it. With so much of our lives and personal information on the web, it’s necessary to have air-tight security to keep it safe. Keep reading to learn more about Remote Browser Isolation and how it works.
Website and PC security are of the utmost importance. Check out our recommendations for the best website security software to add extra protection to your PC.
What is Remote Browser Isolation?
Remote Browser Isolation (RBI) is a security process for web browsing that protects users from internet threats like malware and hacking. RBI differs from local browser isolation, which requires hardware or software elements. RBI is a service from a third-party provider, like Cisco Umbrella.
One of the most common ways cyber hackers get malware to unsuspecting users is through phishing emails. These are scam emails that contain a link to a website with malicious code that is embedded in the webpage.
This code can steal personal information and invade the user’s computer. RBI is designed to protect users from this.
What are the key benefits of browser isolation?
1. Provides top-notch security
Browser isolation gives users protection from malicious websites and links because any local code and URLs open on a remote server and thus don’t take place on the user’s personal PC. This security also extends to emails to protect against phishing as all web-based emails are rendered on the server.
The isolated browser service also prevents any malicious files from downloading on a computer. All downloads are scanned to detect any threats before they are permitted to be downloaded to a PC.
Advanced anonymous browsing features protect users from trackers and hide browsing activity from cybercriminals. It operates like a private browsing window and clears any cookies and history after ending a browsing session.
2. Protects personal information
One of the major key benefits of RBI is the protection of user data like addresses, passwords, identification numbers, etc. Users can have peace of mind when entering their personal or sensitive information online as there is no local data caching.
RBI operates using a Zero Trust security model. This model trusts nothing and no one, including users, applications, and websites. Zero Trust architecture requires strict verification of every entity using a private network.
3. Uses fewer PC resources
Because the isolation happens remotely rather than locally directly from a user’s PC, it uses up fewer computer resources. All the resources needed come from the remote servers and therefore provide air-tight security while being extremely lightweight on PCs.
Are there any drawbacks to RBI?
One of the main drawbacks to an RBI service is the cost. Detecting malware on webpages and rendering sites in pixels is a resource-heavy task and thus can be expensive. Luckily most services provide free demos for companies to try before they commit.
Large organizations and companies use these services especially when employees deal with sensitive information and require extra protection.
Because there is no local data caching and RBI operates on a Zero Trust security model, data like usernames, passwords, addresses, etc. are not saved. This means users must manually enter their information on websites each time. Auto-fill makes browsing faster and easier, but it is also a security risk that RBI eliminates.
How many types of browser isolation are there?
There are three main types of browser isolation: client-side, on-premise, and remote. Here’s a closer look at each type.
- Client-side browser isolation loads web pages and codes directly from a user’s device. Sandboxing keeps code and content separate so any malware doesn’t compromise a PC. This uses up more computer resources than with RBI.
- On-premise browser isolation operates like RBI but rather than content going through a remote server, it takes place on an internal server managed by your organization.
- Remote Browser Isolation or sometimes known as cloud-hosted browser isolation creates an isolated environment on a remote server in a cloud. Within RBI, there are two main ways to isolate a device: DOM mirroring and pixel reconstruction.
- DOM mirroring filters out specific types of content before it reaches a user. This technique prevents content considered dangerous from getting to a user’s device while displaying content deemed safe.
- Pixel reconstruction, or visual streaming, is when the browser runs entirely on the remote server and only displays the pixels of the page to a user. This isolates the browser entirely and the user receives a visual rendering of the content.
RBI offers the same level of security as local browser isolation but is much more lightweight on user computers. Because webpages and code are executed on a remote cloud server, nothing takes place on your device.
How does Remote Browser Isolation work?
Users fall victim to malicious websites because their browser will run the code thinking it’s legitimate. RBI prevents this code from executing by running in a sandboxed state by rendering the webpage in a cloud-based remote server.
When a user visits a webpage with RBI, the page loads on the remote server and provides a rendering of the page and thus eliminating any malicious code. This doesn’t impact how the page operates or its features so users can browser normally while remaining secure.
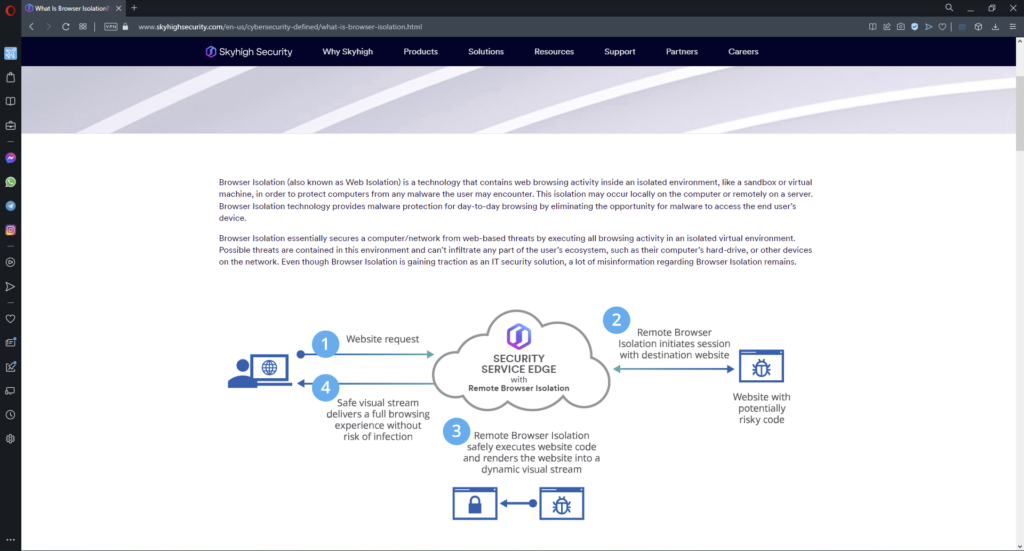
Not every webpage you visit renders on a remote server. If RBI detects potential malware on a page it will evaluate it to detect anything malicious. If it does detect something wrong, then the webpage will load through the remote isolated browser.
The content that the user sees through their default browser is a collection of pixels on an HTML5 base instead of the code that renders the page.
We hope you enjoyed our guide on Remote Browser Isolation and how it functions. For more information on security tips and tricks, check out our guide on the best security settings for Windows 11 for maximum security. Let us know in the comments what you think of RBI or if you already use it.